How can Dos attacks be mitigated?
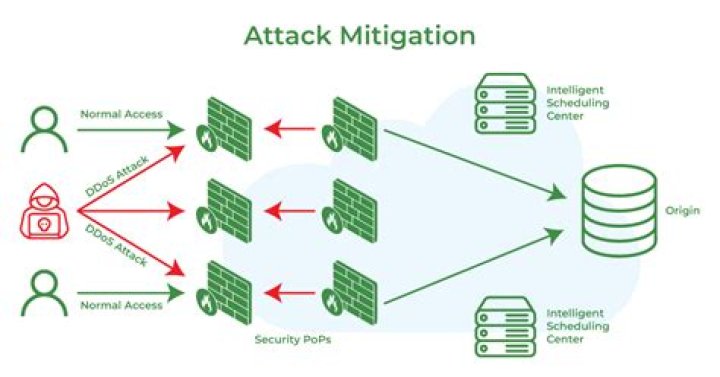
Most common mitigation techniques work by detecting illegitimate traffic and blocking it at the routing level, managing and analyzing the bandwidth of the services, and being mindful when architecting your APIs, so they’re able to handle large amounts of traffic.
How does DDoS mitigation work?
Specifically, DDoS protection works by using algorithms and advanced software to monitor incoming traffic to the website. Any traffic that isn’t legitimate is denied access, whereas legitimate traffic continues to filter through to the site. DDoS protection options generally guard against attacks up to certain size.
What is IP scrubbing?
A scrubbing server is a dedicated machine that receives all network traffic destined for an IP address and attempts to filter good traffic from bad. Ideally, the scrubbing server will only forward non-DDoS packets to the Internet application being attacked.
Is TCPShield only for Minecraft?
Can you protect things other than Minecraft? In the future we have considered this, but at this time we are only able to protect Minecraft servers. If you need web protection we recommend using Cloudflare as a free alternative.
What is DDoS Minecraft?
The goal of DDoS in Minecraft is to try and frustrate users on a rival server with slow service — so that they end up switching to yours. OVH offers Minecraft DDoS mitigation services and, in September 2016, it suffered a crushing DDoS attack unlike anything it had seen before.
What is do’s protection?
Denial of service protection or DoS protection is a tactic implemented by organizations to guard their content network against DoS attacks, which flood a network with server requests, slowing overall traffic functionality and eventually causing long term interruptions.
What is DDoS scrubber?
DDoS Scrubbing Features The Stream DDoS Scrubbing service protects all of your Internet traffic from DDoS attack. Scrubbing means that you stay online during attacks without losing service. Live traffic is analysed with malicious traffic removed and clean traffic passed on for delivery.
How to stop DDoS attacks?
Identify the DDoS attack early. If you run your own servers,then you need to be able to identify when you are under attack.
How to prevent DDoS attacks on a router?
Use a firewall. Use antivirus software. Use a Virtual Private Network (VPN). Keep your operating system up to date. Keep your hardware and software up to date. Use official servers for online gaming. Only take voice chats from people you know. Reset your IP address. See More…
How to report a DDoS attack?
1) Contact your web hosting service if you do not host your own website. 2) Call your internet provider if you do host your own web servers. 3) Explain that you are currently the victim of a DDoS attack. If possible, tell them what type of protocol is overwhelming your system. 4) Follow the provider’s instructions to mitigate the attack. Mitigation is the process of stopping or reducing the damage of the attack.
What is DDoS mitigation?
DDoS mitigation is a set of techniques or tools for resisting or mitigating the impact of distributed denial-of-service (DDoS) attacks on networks attached to the Internet by protecting the target and relay networks.