How do I get the HMAC key?
Creating an HMAC key
- In the Google Cloud Console, go to the Cloud Storage Browser page. Go to Browser.
- Click Settings.
- Select the Interoperability tab.
- Click + Create a key for a service account.
- Select the service account you want the HMAC key to be associated with.
- Click Create key.
How do I create a HMAC token?
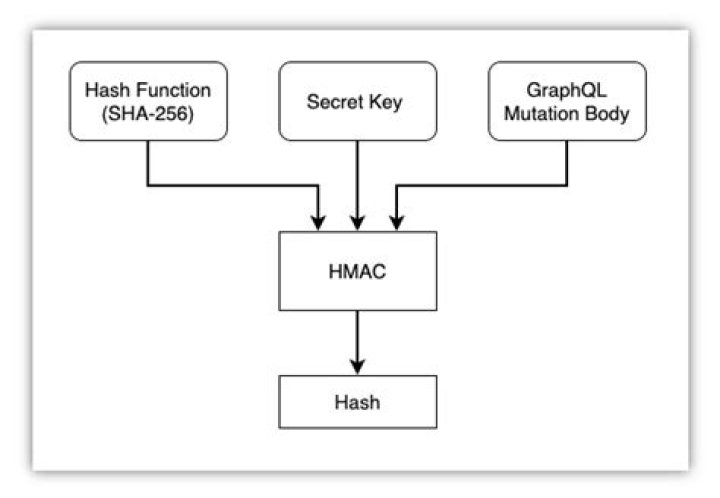
First, enter the plain-text and the cryptographic key to generate the code. Then, you can use select the hash function you want to apply for hashing. The default is SHA-256. Then you can submit your request by clicking on the compute hash button to generate the HMAC authentication code for you.
How is HMAC calculated?
HMAC uses two passes of hash computation. The secret key is first used to derive two keys – inner and outer. The first pass of the algorithm produces an internal hash derived from the message and the inner key. The second pass produces the final HMAC code derived from the inner hash result and the outer key.
How do I create a signature in HMAC?
Setting up HMAC using the Dashboard Scroll to the Authentication options. Select HMAC (Signed Authetication Key) from the drop-down list. Configure your HMAC Request Signing settings. Select Strip Authorization Data to strip any authorization data from your API requests.
How do I decrypt HMAC?
HMAC is a MAC/keyed hash, not a cipher. It’s not designed to be decrypted. If you want to encrypt something, use a cipher, like AES, preferably in an authenticated mode like AES-GCM. The only way to “decrypt” is guessing the whole input and then comparing the output.
Is HMAC a KDF?
HKDF is a simple key derivation function (KDF) based on HMAC message authentication code. It was initially proposed by its authors as a building block in various protocols and applications, as well as to discourage the proliferation of multiple KDF mechanisms.
Can you reverse HMAC?
What is AES and SHA?
SHA stands for Secure Hash Algorithm while AES stands for Advanced Encryption Standard. So SHA is a suite of hashing algorithms. AES on the other hand is a cipher which is used to encrypt.
What is Bcrypt password?
bcrypt is a password-hashing function designed by Niels Provos and David Mazières, based on the Blowfish cipher and presented at USENIX in 1999. The bcrypt function is the default password hash algorithm for OpenBSD and was the default for some Linux distributions such as SUSE Linux.
How to generate HMAC with HMAC generator?
Best HMAC Generator Online Tool with SHA256, MD5, SHA1 and More… Hash-based Message Authentication Code (HMAC) generator uses Algorithms and secret key to generate the HMAC. How to Generate HMAC? Step 1: Select the Algorithms. Such as SHA256, SHA1, MD5. Step 2: Enter the Key. Step 3: Enter the Plain or Cypher Text. What is HMAC?
What is HMAC and secret key?
A HMAC is a small set of data that helps authenticate the nature of message; it protects the integrity and the authenticity of the message. The secret key is a unique piece of information that is used to compute the HMAC and is known both by the sender and the receiver of the message.
What does HMAC stand for?
HMAC Generator / Tester Tool. Computes a Hash-based message authentication code (HMAC) using a secret key. A HMAC is a small set of data that helps authenticate the nature of message; it protects the integrity and the authenticity of the message.
Can I use HMAC SHA256 online?
The HMAC might be founded on message-digest calculations along with the SHA256, MD5 etc. Ownership of an HMAC esteem does now not bargain the delicate realities as HMACs aren’t reversible curios. This tool can be used as hmac sha256 online. Buy us a Coffee JSON Formatter FAQ Privacy Policy About Contact History Where am I right now?