How is birthday attack performed on hash functions?
The birthday attack cracks the mathematics algorithm by its matching in the hash function. The birthday attack is best calculated with the probability theory. However, the attack can be prevented by increasing the bit length and if the signer makes some random changes within the document.
What is birthday attack explain with suitable example?
The birthday attack is named after the birthday paradox. If you fail to match, you leave the room and Joe has a 21/365 chance of sharing a birthday with the remaining people. If Joe fails to match, he leaves the room and Morgan has a 20/365 chance, and so on. If you add 22/365 + 21/365 + 20/365 + 19/365 …
How is birthday attack calculated?
However, it is simpler to calculate P(A′), the probability that no two people in the room have the same birthday. Then, because A and A′ are the only two possibilities and are also mutually exclusive, P(A) = 1 − P(A′)….Calculating the probability.
| n | p(n) |
|---|---|
| 60 | 99.4% |
| 70 | 99.9% |
| 75 | 99.97% |
| 100 | 99.99997% |
Why is birthday attack an efficient method for breaching security?
The birthday attack is a statistical phenomenon relevant to information security that makes the brute forcing of one-way hashes easier. It’s based off of the birthday paradox, which states that in order for there to be a 50% chance that someone in a given room shares your birthday, you need 253 people in the room.
How does the birthday problem work?
The birthday paradox, also known as the birthday problem, states that in a random group of 23 people, there is about a 50 percent chance that two people have the same birthday. But when all 23 birthdays are compared against each other, it makes for much more than 22 comparisons.
What is birthday paradox in DAA?
Persons from first to last can get birthdays in following order for all birthdays to be distinct: The first person can have any birthday among 365. The second person should have a birthday which is not same as first person. The third person should have a birthday which is not same as first two persons.
What is a hash collision attack?
In cryptography, a collision attack on a cryptographic hash tries to find two inputs producing the same hash value, i.e. a hash collision. This is in contrast to a preimage attack where a specific target hash value is specified.
Which type of attack can compromise a hash function?
encryption collision attack
A successful encryption collision attack on a cryptographic hash function could compromise the security of all kinds of digital systems.
What is susceptible to birthday attacks?
Digital signatures can be susceptible to birthday attacks. A message m is typically signed by first computing H(m), where H is a cryptographic hash function, and then using some secret key to sign H(m).
Which of the following algorithm is vulnerable to birthday attacks?
S1- MD5 is vulnerable to the Birthday attack.
What is the birthday paradox formula?
The odds are calculated by counting all the ways that N people won’t share a birthday and dividing by the number of possible birthdays they could have. For example, two people could have 365×365 birthday combinations. So the chance that two people don’t share a birthday is (365×364)/365².
How do you prove your birthday paradox?
Let the birthday of person 1 be established. The probability that person 2 shares person 1’s birthday is 1365. Thus, the probability that person 2 does not share person 1’s birthday is 364365. Similarly, the probability that person 3 does not share the birthday of either person 1 or person 2 is 363365.
How to avoid birthday attack of hash function?
To avoid such an attack the output of hash function should be a very long sequence of bits such that birthday attack now becomes computationally infeasible. Attention reader!
What is the chance of collision with 23 hash values?
Given 23 people, we have 50% chance of collision (two people with the same birthday). Hence, if we have that our hash functions maps data to a day in the calendar year. That is, it maps hash(data) -> [0, 364], then given 23 hash values, we have 50% chance for collision.
Should you use hash functions?
If you use it in a cryptographic setup, the answer is Do not use. On the other hand, hash function are often used to calculate identifiers. For that purpose, it also depends if you should use it or not. This is where the Birthday Paradox comes in.
What is a birthday attack?
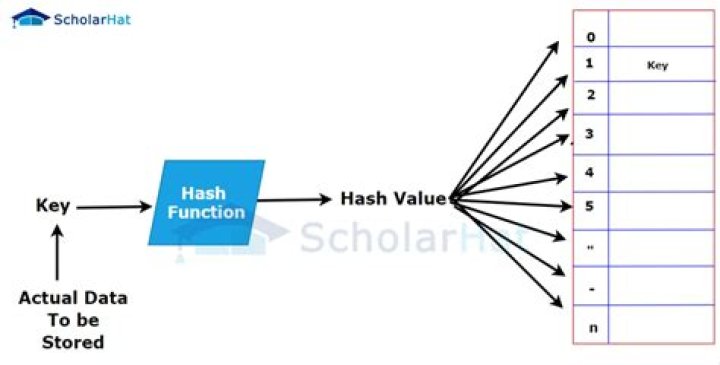
Birthday attack is a type of cryptographic attack that belongs to a class of brute force attacks. It exploits the mathematics behind the birthday problem in probability theory.



