How is MD5 implemented?
MD5 processes a variable-length message into a fixed-length output of 128 bits. The input message is broken up into chunks of 512-bit blocks (sixteen 32-bit words); the message is padded so that its length is divisible by 512. The padding works as follows: first, a single bit, 1, is appended to the end of the message.
What is MD5 in C?
/* md5. c – Functions to compute MD5 message digest of files or memory blocks according to the definition of MD5 in RFC 1321 from April 1992.
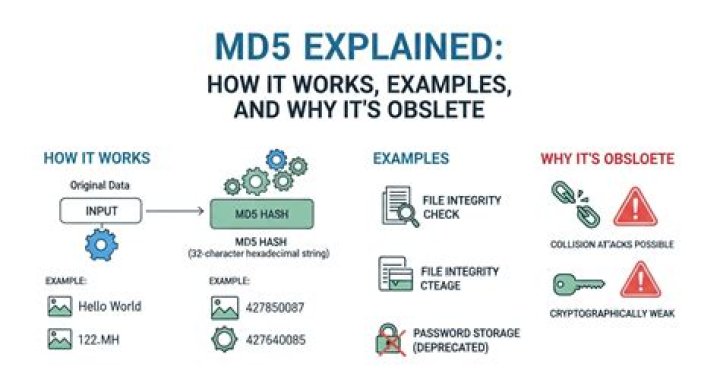
Is MD5 still used?
MD5 is still being used today as a hash function even though it has been exploited for years. Hash functions have variable levels of complexity and difficulty and are used for cryptocurrency, password security, and message security. Following in the footsteps of MD2 and MD4, MD5 produces a 128-bit hash value.
What is replacing MD5?
This is why MD5 is considered cryp-tographically broken and is being replaced by the SHA-2 family of hash functions. MD5 security is certainly not suitable for security-based applications and services like SSL or digital signatures that rely on collision resistance.
How many steps are performed in one round of MD5?
How do the MD5 Algorithm works? As we all know that MD5 produces an output of 128-bit hash value. This encryption of input of any size into hash values undergoes 5 steps, and each step has its predefined task.
What is MD5 and how it works?
The MD5 (message-digest algorithm) hashing algorithm is a one-way cryptographic function that accepts a message of any length as input and returns as output a fixed-length digest value to be used for authenticating the original message.
How do you generate the MD5 hash of a string?
Call MessageDigest. getInstance(“MD5”) to get a MD5 instance of MessageDigest you can use. The compute the hash by doing one of: Feed the entire input as a byte[] and calculate the hash in one operation with md.
What is MD5 used for today?
Can you decrypt MD5?
The MD5 cryptographic algorithm is not reversible i.e. We cannot decrypt a hash value created by the MD5 to get the input back to its original value. So there is no way to decrypt an MD5 password.
What is an acceptable MD5 implementation?
Solutions on this page should implement MD5 directly and NOT use built in (MD5) functions, call outs to operating system calls or library routines written in other languages as is common in the original MD5task. The following are acceptable: An original implementation from the specification, reference implementation, or pseudo-code
What is MD5 algorithm?
For details of the algorithm refer to MD5 on Wikipediaor the MD5 definition in IETF RFC (1321). The implementation needs to implement the key functionality namely producing a correct message digest for an input string. It is not necessary to mimic all of the calling modes such as adding to a digest one block at a time over subsequent calls.
How do you get a readable MD5 hash in Python?
To get a readable hash, you have to concatenate the received buffers using their hexadecimal representation. There is however one last problem. The md5 function uses little-endian buffers. To print them in the correct order, we have to invert bits this time for 32-bit numbers.