What is a zero-day threat?
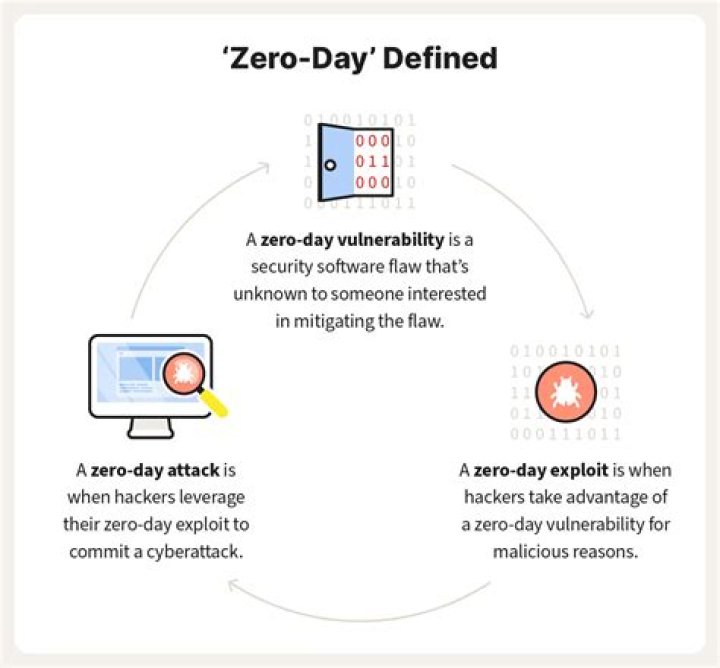
A zero-day threat (also sometimes called a zero-hour threat) is one that hasn’t been seen before and doesn’t match any known malware signatures. This makes it impossible to detect by traditional signature-matching solutions.
Is zero day attack a virus?
Zero day malware is malware that exploits unknown and unprotected vulnerabilities. This novel malware is difficult to detect and defend against, making zero day attacks a significant threat to enterprise cybersecurity.
What is a zero-day exploit with example?
A zero-day (0day) exploit is a cyber attack targeting a software vulnerability which is unknown to the software vendor or to antivirus vendors. Typical targets for a zero-day exploit include: Government departments. Large enterprises. Individuals with access to valuable business data, such as intellectual property.
How are zero days found?
In most cases, hackers use code to exploit zero-day. Sometimes it is discovered by an individual when the program behaves suspiciously, or the developer himself may recognize the vulnerability. Attackers have found a new route by exploiting a zero-day vulnerability in Google’s Android mobile operating system.
Are zero-day attacks common?
According to the Ponemon Institute, 80% of successful breaches were Zero-Day attacks.
How zero-day attack can be detected and prevented?
Anti-virus signatures released – if attackers have created zero-day malware, anti-virus vendors can identify its signature relatively quickly and protect against it. Systems could still be exposed because there may be other ways of exploiting the vulnerability.
How does a zero-day vulnerability differ from malware?
This is when software has a flaw known to the developer, but the developer does not yet have a patch ready to be released. A zero-day exploit is a software package coded to take advantage of the known zero-day vulnerability. In most cases, a zero-day exploit is packaged as malware.
Is there any defense against zero day attacks?
A zero-day (or 0-day) vulnerability is a software vulnerability that is discovered by attackers before the vendor has become aware of it. By definition, no patch exists for zero day vulnerabilities and user systems have no defenses in place, making attacks highly likely to succeed.
Where did the term zero-day come from?
The term “zero-day” actually refers to the number of days the software vendor has been aware of the vulnerability or its exploit. The term originated from the days of digital bulletin boards, when “zero-day” referred to the number of days since a new software program had been released to the public.
What is zero day malware?
Zero-day malware is a specific kind of malware or malicious software that has only recently been discovered. In general, a zero-day phenomenon is one that is not previously known about or anticipated.
What are zero day threats?
Zero-day threats are sometimes known as “day-zero attacks” or “zero-hour attacks”. There’s a timeline associated with zero-day vulnerabilities, sometimes known as the vulnerability window: the period between the first successful exploitation of a flaw or glitch, and the release or application of a successful security patch to counter it.
What is zero day vulnerability?
A zero-day vulnerability is a software security flaw that is known to the software vendor but doesn’t have a patch in place to fix the flaw.
What is zero day bug?
Zero day bug. are basically unfixed bugs or vulnerabilities in software. hacker digs out bugs in a software that even the developers are unaware of. the attacker creates tools to exploit the bug and attack the system through it.