What is eavesdropping in wireless network?
An eavesdropping attack occurs when a hacker intercepts, deletes, or modifies data that is transmitted between two devices. Eavesdropping, also known as sniffing or snooping, relies on unsecured network communications to access data in transit between devices.
How eavesdropping can harm your system?
An eavesdropping attack, also known as a sniffing or snooping attack, is a theft of information as it is transmitted over a network by a computer, smartphone, or another connected device. The attack takes advantage of unsecured network communications to access data as it is being sent or received by its user.
What are the challenges of wireless sensor networks?
Challenges in such WSN include high bandwidth demand, high energy consumption, quality of service (QoS) provisioning, data processing and compressing techniques, and cross-layer design.
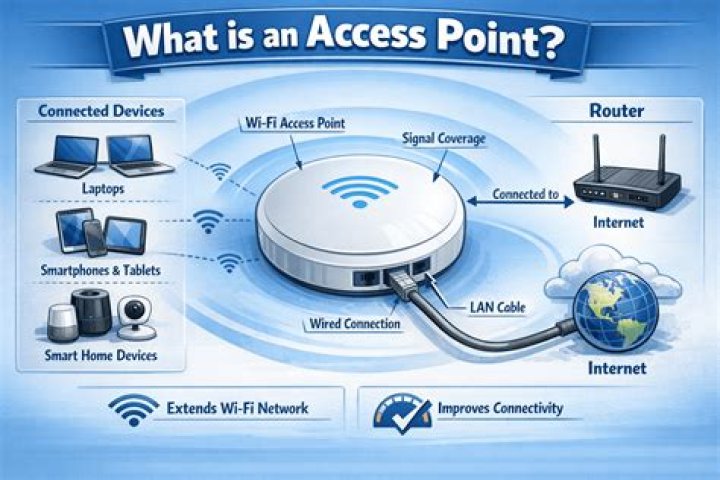
How does WiFi eavesdropping work?
What is WiFi Eavesdropping? WiFi Eavesdropping can involve a hacker stealing data while on a public, unsecured wifi network. The unsecured transmission of data allows for the theft of anything that’s unencrypted, from passwords to files to financial information (both personal and business-related).
What is the purpose of eavesdropping?
Eavesdropping is commonly applied to discover the contents of confidential communication. In particular, eavesdropping is often used to intercept personal communication (e.g., email or instant messages) or authentication credentials. When applied to the telephone network, eavesdropping is also called wiretapping.
Which topology is used in wireless sensor network?
star network topology
The star network topology is one of the most common sensor network topologies. A wireless personal area network (WPAN), consisting of a smartphone connected to several wireless sensors, is a common example of this topology.
Where are wireless sensors used?
Wireless Sensor Network Applications Sensor nodes are used for constant sensing, event ID, event detection & local control of actuators. The applications of wireless sensor networks mainly include health, military, environmental, home, & other commercial areas.
Why is it called eavesdropping?
Eavesdrop started off literally: first it referred to the water that fell from the eaves of a house, then it came to mean the ground where that water fell. Eventually, eavesdropper described someone who stood within the eavesdrop of a house to overhear a conversation inside.