What is shellcode in buffer overflow?
Shellcode is considered exploit code or exploit payload. Buffer overflows are the most popular way of injecting a shellcode1 because after the instructions of the called function are done executing, the executable code that the adversary placed on the stack will begin executing.
What is a shellcode attack?
The term “shellcode” was historically used to describe code executed by a target program due to a vulnerability exploit and used to open a remote shell – that is, an instance of a command line interpreter – so that an attacker could use that shell to further interact with the victim’s system.
What happens during shellcode injection?
Simply put, shellcode injection is a hacking technique where the hacker exploits vulnerable programs. The hacker infiltrates into the vulnerable programs and makes it execute their own code.
What is shellcode in cyber security?
Shellcode is a special type of code injected remotely which hackers use to exploit a variety of software vulnerabilities. It is so named because it typically spawns a command shell from which attackers can take control of the affected system.
What is shellcode written in?
machine code
Shellcode is commonly written in machine code. When creating shellcode, it is generally desirable to make it both small and executable, which allows it to be used in as wide a variety of situations as possible. Writing good shellcode can be as much an art as it is a science.
What is shellcode loader?
Shellcode Loader Engine for Windows. This makes testing and debugging shellcode easier. This is quite simple shellcode loader which simply loads shellcode (binary file) in memory and runs it.
Why is shellcode written in assembly?
Since there is often limited space to work with in the buffer, shellcode is often designed to be as short as possible, thus it is often written by hand in assembly and dumped to an escaped bytes sequence (e.g. “”).
How is shellcode used in cyber attacks?
Remote shellcode is used when an attacker wants to target a vulnerable process running on another machine on a local network, intranet, or a remote network. If successfully executed, the shellcode can provide the attacker access to the target machine across the network.
What is malicious shellcode detection?
Description. This indicates the detection of malicious shellcode within the network. Shellcode is a special type of code used in the exploitation of many vulnerabilities. It usually spawns a command shell from which attackers can control the compromised system.
Is using Kali Linux illegal?
Kali Linux OS is used for learning to hack, practicing penetration testing. Not only Kali Linux, installing any operating system is legal. If you are using Kali Linux as a white-hat hacker, it is legal, and using as a black hat hacker is illegal.
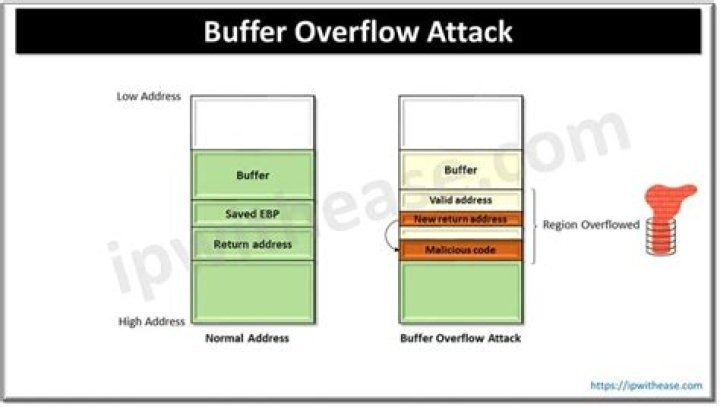
How does a typical buffer overflow exploit work in code?
How does a typical buffer overflow exploit work in code, at run-time and in memory and what can be achieved by running it? A buffer overflow occurs when a program or process attempts to write more data to a fixed length block of memory (a buffer), than the buffer is allocated to hold.
What is shellcode and how can it be used to attack?
With a comprehensive security solution that uses machine learning to identify malicious behavior, attacks by shellcode are seen just like any other attack and stopped before they can do any damage. In this post, we’ve taken a look at what shellcode is and how hackers can use it as malicious input to exploit vulnerabilities in legitimate programs.
What happens if input is too long in shellcode?
This is a programming error, as code should always check first that the length of any input data will not exceed the size of the buffer that’s been allocated. When this happens the program may crash, but specially-crafted input like our shellcode may instead allow an attacker to execute their own code.
How do I overflow a stack in Linux?
Overflowing the Stack In a Terminal window, execute this command. Note: the “$(cat e1)” portion of this command prints out the contents of the e1 file and feeds it to the program as a command-line argument. A more common way to do the same thing is with the input redirection operator: “./bo1 e1”.