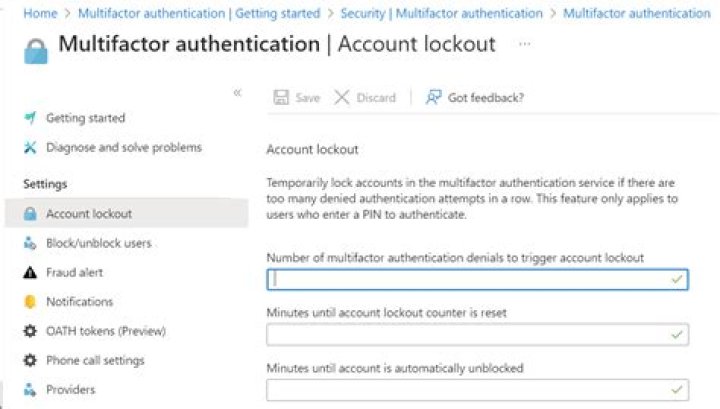
What is the event ID for account lockout?
Event ID 4740
Windows generates two types of events related to account lockouts. Event ID 4740 is generated on domain controllers, Windows servers, and workstations every time an account gets locked out. Event ID 4767 is generated every time an account is unlocked.
How do I find out what caused ad lockout?
How to: Trace the source of a bad password and account lockout in AD
- Step 1: Download the Account Lockout Status tools from Microsoft.
- Step 2: Run ‘LockoutStatus.exe’
- Step 3: Choose ‘Select Target’ from the File menu.
- Step 4: Check the results.
- Step 5: Check the Security log on one of these DCs.
What is UAC value 0x15?
New UAC Value: 0x15. User Account Control: Account Disabled. ‘Password Not Required’ – Enabled. ‘Normal Account’ – Enabled.
How do I view Active Directory logs?
How to View AD Logs in Event Viewer or Netwrix Auditor
- Open the Group Policy Management console (gpmc.
- Navigate to Domain Controllers.
- In the Group Policy Management Editor, choose Computer Configuration → Go to Policies → Go to Windows Settings → Go to Security Settings → Go to Local Policies → Go to Audit Policy.
What is the PDC emulator?
PDC Emulator: The DC with the Primary Domain Controller Emulator role is the authoritative DC in the domain. The PDC Emulator responds to authentication requests, changes passwords, and manages Group Policy Objects. And the PDC Emulator tells everyone else what time it is!
Why is my AD account locked?
The purpose behind Active Directory Account Lockout is to prevent attackers from brute-Force attempts to guess a user’s password–too many bad guess and you’re locked out.
How do I fix AD account lockout?
Start –> Run –> Type Control UserPasswords2 , click on Advanced managed passwords and delete all the passwords. Check the third party software installed on client side. If it’s not required, uninstall. Open the Task Scheduler (Run –> Tasks) and delete unwanted tasks.
What is the account Lockout event?
This event generates every time a user account is locked out. For user accounts, this event generates on domain controllers, member servers, and workstations. Note For recommendations, see Security Monitoring Recommendations for this event.
How do I find a locked out account in Windows Server 2003?
Windows Server 2003 log the event with ID 644 for user account locked out . Finding Locked Out Accounts using PowerShell. search-adaccount -u -l | ft name,lastlogondate -auto. Search the Windows Event Logs for the Lockout Event using PowerShell .
How to search for Account Locked Out events in eventcombmt?
The Account Lockout and Management tools contains a utility called EVENTCOMBMT.EXE. There is a builtin search for searching for ACCOUNT LOCKED OUT events. In EventcombMT’s events are for 2003; you need to add the 2008 event if your DCs are 2008.
What does the Windows Event ID 4740 mean?
Windows event ID 4740 – A user account was locked out. Introduction. Windows lets you set an account lockout threshold to define the number of times a user can attempt to log on with an invalid password before their account is locked. You can also define the amount of time an account stays locked out with the account lockout duration setting.