Which hashing function is best?
If you just want to have a good hash function, and cannot wait, djb2 is one of the best string hash functions i know. it has excellent distribution and speed on many different sets of keys and table sizes. you are not likely to do better with one of the “well known” functions such as PJW, K&R[1], etc.
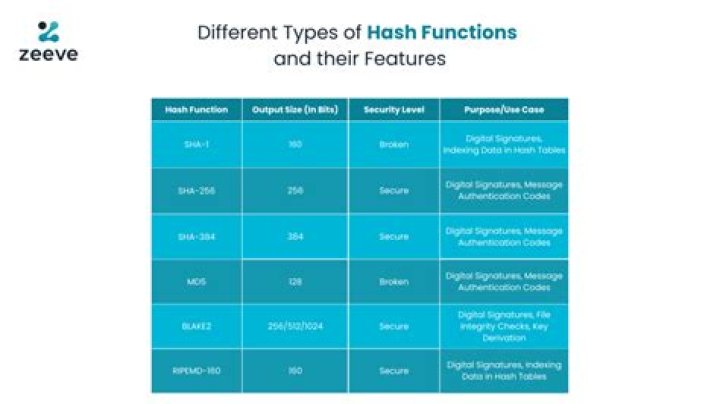
Which hash functions are recommended now?
Google recommends using stronger hashing algorithms such as SHA-256 and SHA-3. Other options commonly used in practice are bcrypt , scrypt , among many others that you can find in this list of cryptographic algorithms.
What are some common uses for hashing?
Applications of Hashing
- Message Digest.
- Password Verification.
- Data Structures(Programming Languages)
- Compiler Operation.
- Rabin-Karp Algortithm.
- Linking File name and path together.
Which is better MD5 or sha256?
As a whole, SHA-256 is better than MD5 because the output size is twice longer and the probability of collisions is lower. SHA-256 is a bit slower than MD5, but it shouldn’t impact performances enough to not use it.
How do I find the best hash function?
Choosing a good hashing function, h(k), is essential for hash-table based searching. h should distribute the elements of our collection as uniformly as possible to the “slots” of the hash table. The key criterion is that there should be a minimum number of collisions. will provide uniform hashing.
Which hash function is fastest?
SHA-1 is fastest hashing function with ~587.9 ms per 1M operations for short strings and 881.7 ms per 1M for longer strings. MD5 is 7.6% slower than SHA-1 for short strings and 1.3% for longer strings.
What is a hash function used for?
Hash functions are used for data integrity and often in combination with digital signatures. With a good hash function, even a 1-bit change in a message will produce a different hash (on average, half of the bits change). With digital signatures, a message is hashed and then the hash itself is signed.
Is sha2 broken?
NEW YORK, NEW YORK, UNITED STATES, September 3, 2019 / — The Wall Street fintech Treadwell Stanton DuPont broke silence today as it announced its Research & Development and Science Teams successfully broke the SHA-256 hashing algorithm silently in controlled laboratory conditions over a year ago.
Which checksum algorithm is best?
SHA512 is currently a good bet. It is possible, and often sensible, to use multiple algorithms. For example, you might compute both MD5 and SHA256 for your files.
What are hash tables and functions?
Associative arrays: Hash tables are commonly used to implement many types of in-memory tables. Database indexing: Hash tables may also be used as disk-based data structures and database indices (such as in dbm). Caches: Hash tables can be used to implement caches i.e. auxiliary data tables that are used to speed up the access to data, which is primarily stored in slower media.
What exactly is a hash function?
A hash is a function that meets the encrypted demands needed to solve for a blockchain computation.
What is the standard hash function?
There is no standard hash function, but the best hash function that you can use in a particular scenario/use case. Usually, its the SHA(1 or 256) algorithms, however, in older and less secure (or non-security related) MD5 is used. Alternatively, hashes can be used informally as CRCs, in which case there are many uses and types.
What is an example of a hash function?
If the hash values are the same, it is likely that the message was transmitted without errors. One example of a hash function is called folding. This takes an original value, divides it into several parts, then adds the parts and uses the last four remaining digits as the hashed value or key.